“The lack of care being taken to correctly configure cloud environments has once again been highlighted by two serious data leaks in the UK caused by misconfigured Amazon Simple Storage Service (S3) bucket storage”.
2019 has been a year of shocking security breaches in the cloud, a trend that will only continue unless businesses make a significant course correction. Gartner recently updated their evaluation of cloud security and concluded: “Through 2025, 99% of cloud security failures will be the customer’s fault.”
By reading the above statements you must have already thought of what we will be discussing in this article. When you start thinking of moving to or building your infrastructure in the cloud, you should do thorough research on the “AWS Shared Responsibility Model” and follow the “AWS Well-Architected Framework” to secure and make your infrastructure perfect.
AWS is responsible for the security and compliance ‘of’ the Cloud, where the customer is responsible for security and compliance ‘in’ the Cloud.
Let us try to understand the “shared responsibility model” by taking the example of your office building and the particulars you have inside your office. Here, the Office building is AWS Cloud, which protects the building, parking, and mailboxes. What is inside the office means inside the cloud say securing your data, computers, users are your responsibility.

Applying the above-illustrated example to AWS cloud-based solutions, AWS’ responsibility of security “of” the Cloud includes hardware, global infrastructure, and how regions, availability zones, and edge locations function and operate. It also encompasses the infrastructure software responsible for compute, storage, database, and network services. AWS customers are responsible for security “in” the Cloud, or what they bring into it. This includes network configurations, customer-controlled encryption, identity and access management (IAM), applications, and customer data.
In the above picture, the first type of responsibility model is “Infrastructure Services”.
Here, AWS owns only the base model say in EC2 they are responsible for underlying infrastructure, compute capacity, and network-related configurations. You being the service user are responsible for configuring the operating system, application software, and defining how your software interacts with other components. In this way, Amazon EC2 is considered an infrastructure service.
Moving on will look into “Container Services”.
Consider the example of using RDS – Relational Database Service for which AWS provides a variety of database engines such as Amazon Aurora, PostgreSQL, MySQL, Oracle, and others. Here, you are purchasing a pre-packaged solution. You are responsible for its configuration and how it is accessed, but you are not responsible for the internals of how it works or functions. You can consider this a containerized type of service where the internals are available for you to configure.
The last model is “Managed Services”.
AWS S3 – Simple Storage Service, while using the S3 service you would be only responsible for the data in the bucket and encryption of it. The rest of the things such as hardware, software configurations, network, storage space, and other things will be of AWS’s responsibility.
“As customers keep moving towards managed services their responsibilities will be reduced”. Moving towards managed services helps you focus more on innovation and businees goals.
The breadth of AWS services enables solution builders the flexibility to choose between highly customizable options with greater customer responsibility or fully managed services requiring less customer responsibility beyond the basic configuration. In this way, AWS provides undifferentiated heavy lifting, not only for infrastructure and solution creation but also for compliance documentation and practices.
AWS Well-Architected Framework
A well-Architected framework helps cloud architects build secure, high-performing, resilient, and efficient infrastructure for their applications and workloads.
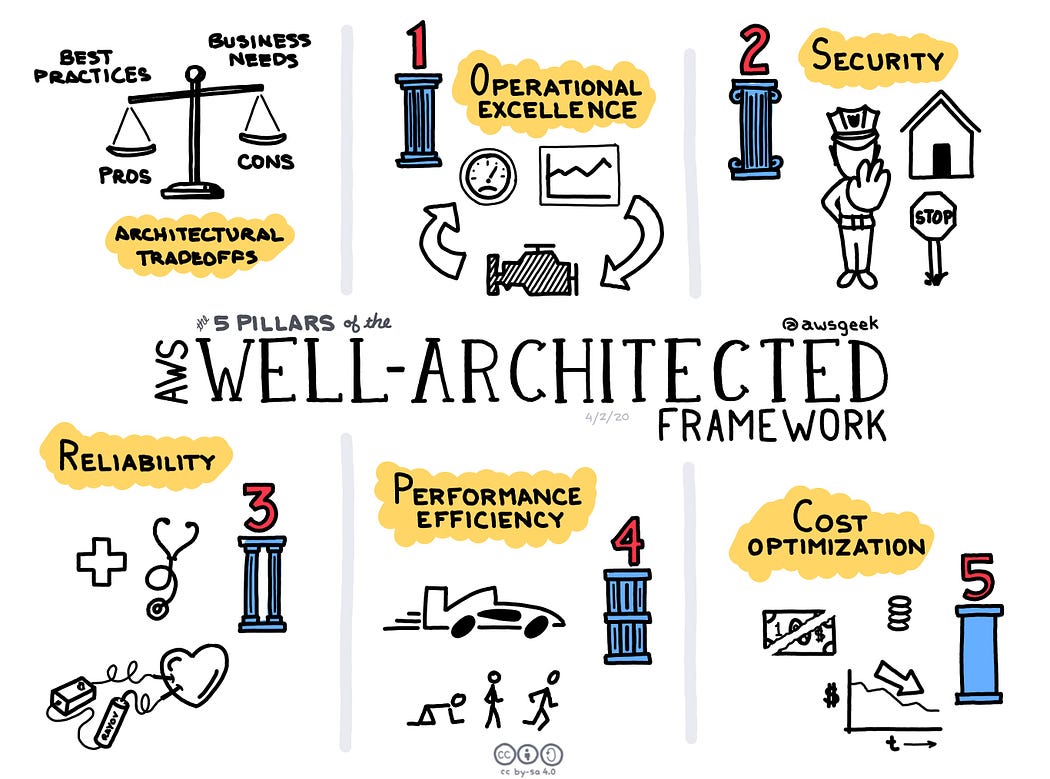
It is built on 5 pillars – Operational Excellence, Security, Reliability, Performance Efficiency, and Cost optimization.
Operational Excellence Pillar: This pillar focuses on running and monitoring systems to deliver business value, and continually improving processes and procedures. Key concepts are automatic changes, responding to events, and defining standards to manage daily operations.
Security Pillar: It focuses on securing and keeping your data away from threats. Key concepts include using security services, managing who can do what with privilege management, and establishing controls to detect security events.
Reliability Pillar: Consistency is the key in this pillar. A resilient workload quickly recovers from failures to meet business and customer demand. Key topics include distributed system design, recovery planning, and how to handle change.
Performance Efficiency Pillar: Efficient usage of IT and computing resources is the key focus in this pillar. selecting the right resource types and sizes based on workload requirements, monitoring performance, and making informed decisions to maintain efficiency as business needs evolve.
Cost optimization Pillar: Selecting the most appropriate and right number of resource types, analyzing spend over time, and scaling to meet business needs without overspending are the key focus in this pillar.
Conclusion
Research on the Shared responsibility model and Well architected framework will help you in analyzing and building your Cloud infrastructure in the best possible way. Implementing these methodologies will make sure your Cloud environment is Safe, Secure, Reliable, and Highly efficient.